The Truth Behind Counterfeit Stock — The Local Artisan Guide

Ransomware-as-a-service: Understanding the cybercrime gig ec - vulnerability database

Malware Posing as Russia DDoS Tool Bites Pro-Ukraine Hackers - vulnerability database
oregonnews/core/fixtures/jamaica_sample.json at master · uoregon-libraries/oregonnews · GitHub
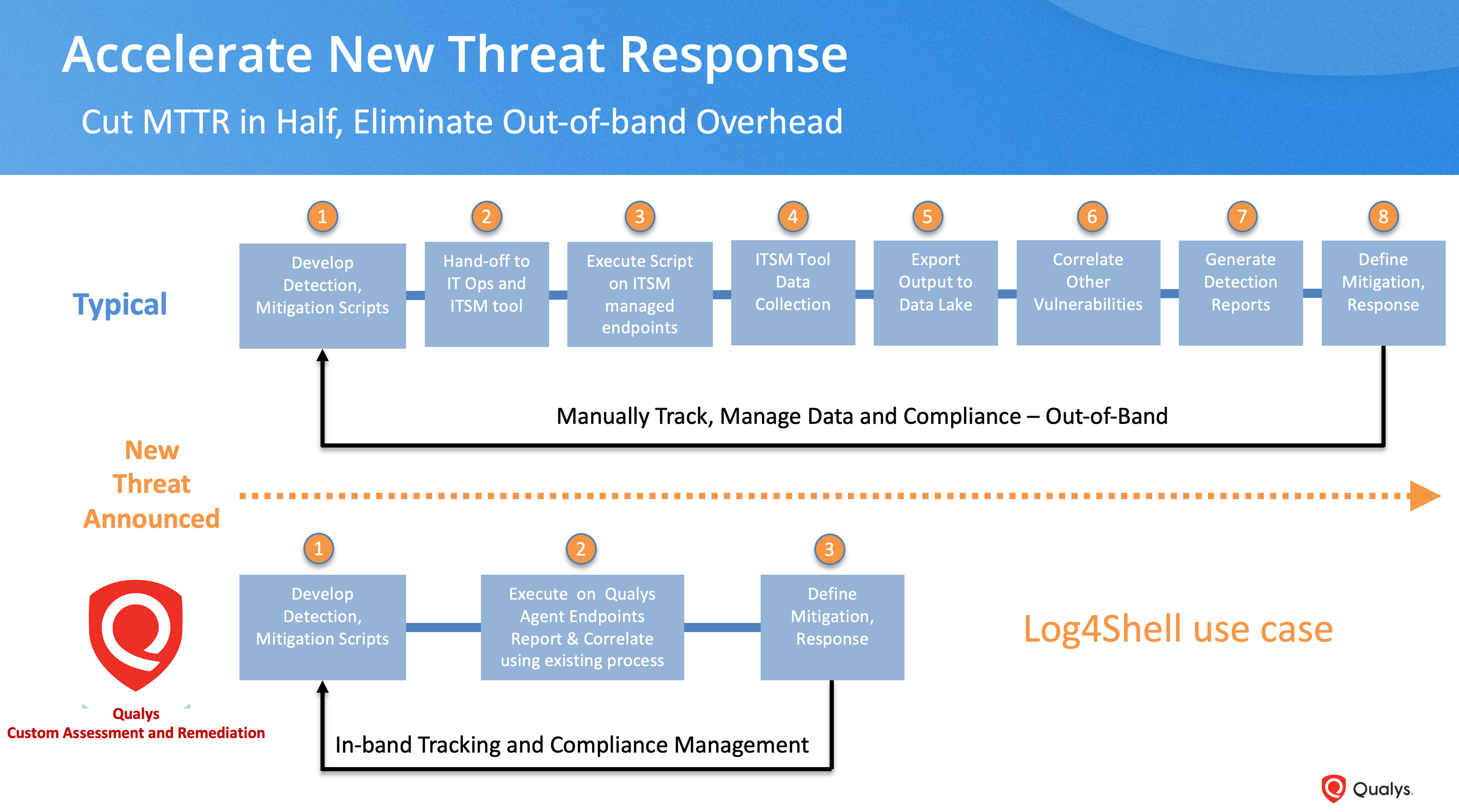
What's Next After Log4Shell? - vulnerability database
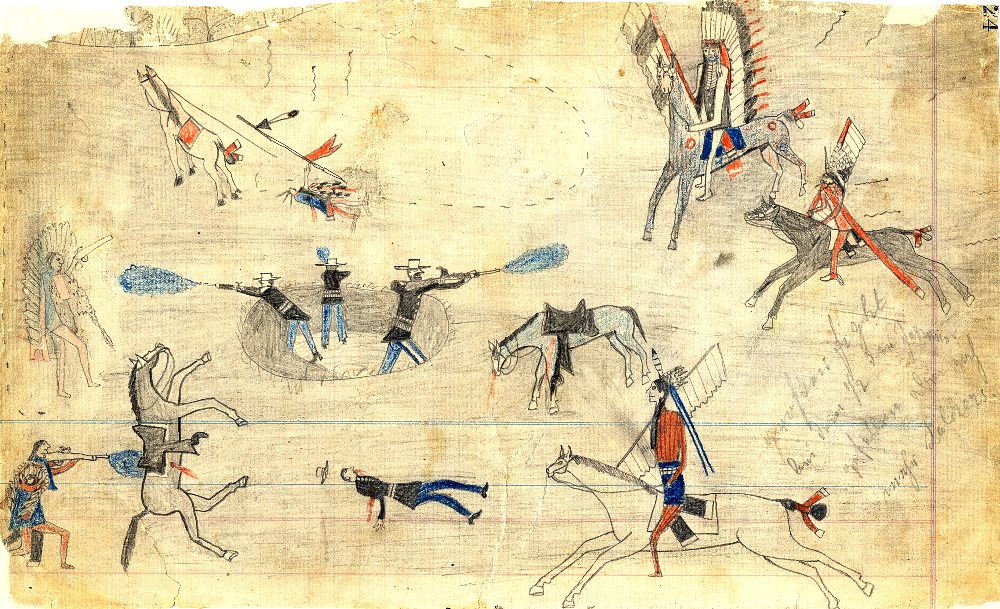
How Possibly Fraudulent and Forged Indigenous Art Ends up in Museums
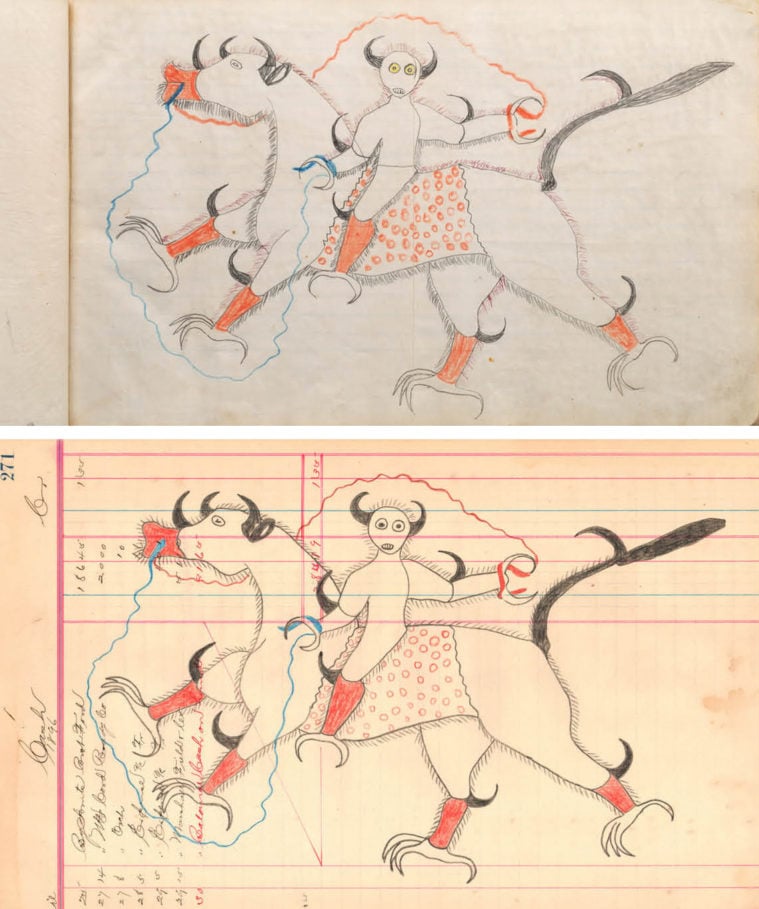
How Possibly Fraudulent and Forged Indigenous Art Ends up in Museums

OWASSRF, a new exploit for Exchange vulnerabilities, exploit - vulnerability database

RCE Bugs in Hugely Popular VoIP Apps: Patch Now! - vulnerability database
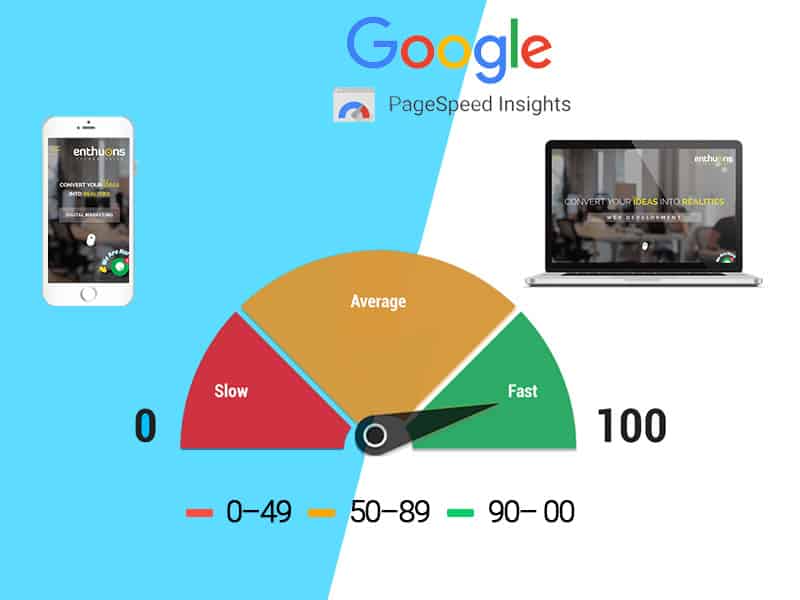
What Is Google Page Speed & Website load time
Update on the Confluence 0-day vulnerability (CVE-2022-26134) - vulnerability database
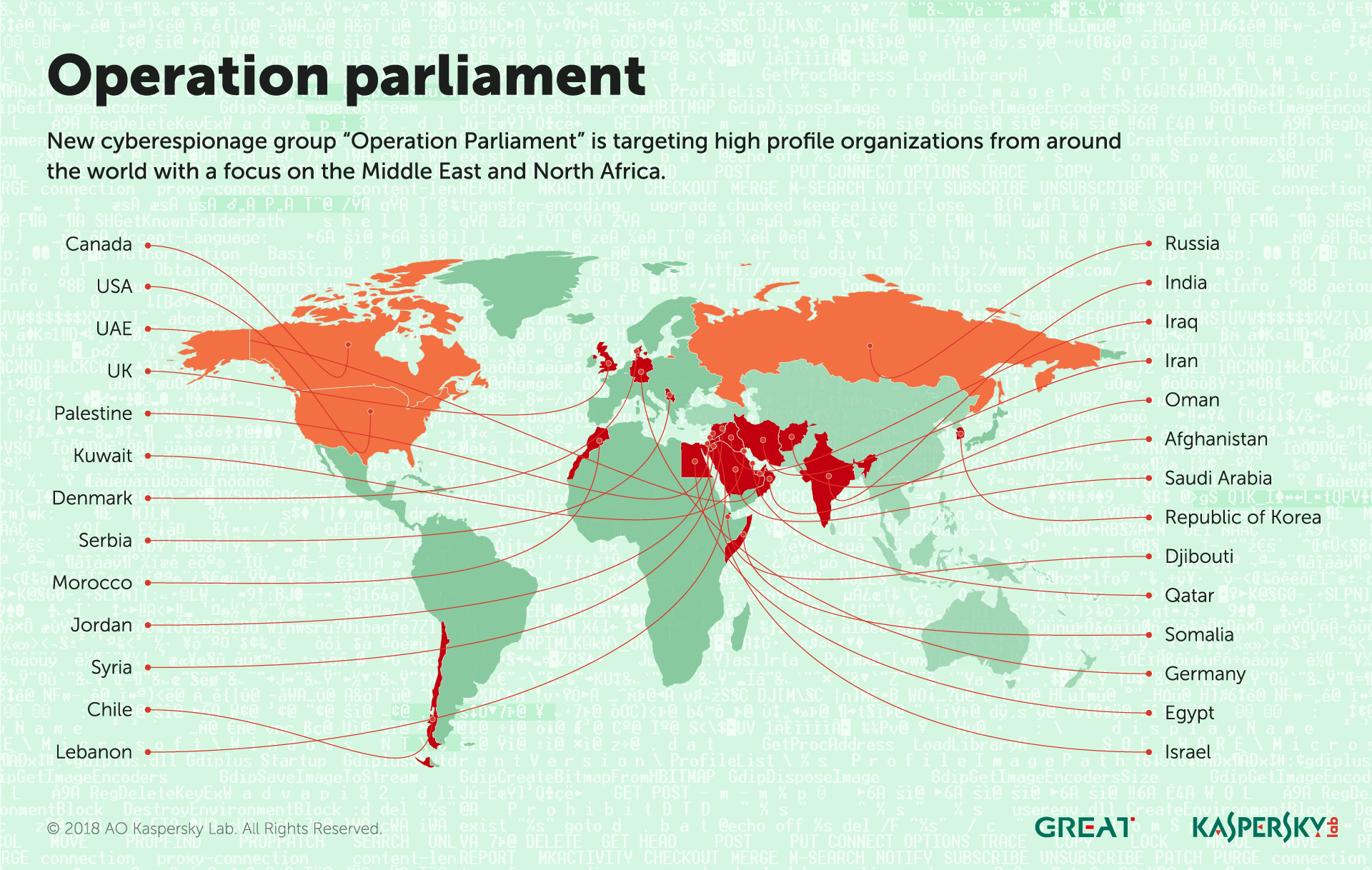
IT threat evolution Q2 2018 - vulnerability database
slang/src/assets/data/fuck_long_data_censored.json at master · the-pudding/slang · GitHub
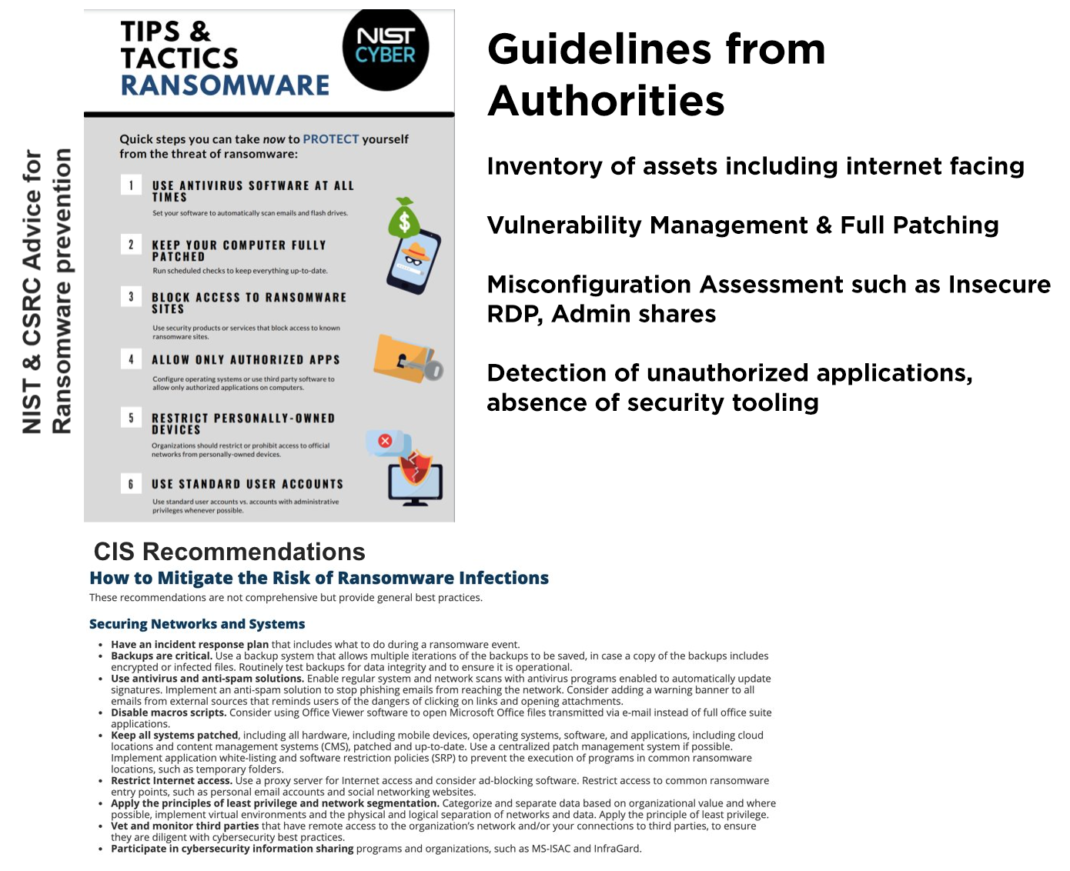
Assess Your Risk From Ransomware Attacks, Powered by Qualys - vulnerability database

How Possibly Fraudulent and Forged Indigenous Art Ends up in Museums
The Truth Behind Counterfeit Stock — The Local Artisan Guide
- Best Price $ 69.99. Good quality and value when compared to lesalarie.ma similar items.
- Seller - 480+ items sold. Top-Rated Plus! Top-Rated Seller, 30-day return policy, ships in 1 business day with tracking.
People Also Loved
-

Louis Vuitton Fragrance Rose Des Vents
Buy It Now 22d 7h -

Best 25+ Deals for Louis Vuitton Neverfull Mm Damier
Buy It Now 17d 16h -

Louis Vuitton Brown Spirit Nano Monogram Bracelet 17 Louis Vuitton
Buy It Now 5d 17h -

Nike Airforce 1 Low X TRAVIS SCOTT X LOUIS VUITTON – SNEAKS.FREAKS
Buy It Now 5d 20h -

Louis Vuitton White Multicolore Sologne Bag - Yoogi's Closet
Buy It Now 8d 12h -

Women's Designer Bags & Purses - Luxury Handbags
Buy It Now 4d 11h -

Lauren Conrad Blue Crossbody Purse for Sale in Mission Viejo, CA - OfferUp
Buy It Now 13d 15h -

goyard anjou gm bag|TikTok Search
Buy It Now 9d 21h -

Four Louis Vuitton Crossbody Bags You Need Now
Buy It Now 10d 11h -

Case Study: Creating a new audio experience inside Louis Vuitton stores • Hotel Designs
Buy It Now 26d 19h -

Speedy BANDOULIÈRE
Buy It Now 15d 15h -

How To Spot A Real Louis Vuitton Montsouris Backpack
Buy It Now 3d 11h -

Shop Louis Vuitton Boulogne (M45831, M45832) by luxurysuite
Buy It Now 24d 14h -

LV Trainer Sneaker - Shoes
Buy It Now 13d 11h -

Louis Vuitton LV Shadow Dragonne Key Holder and Bag Charm Blue Metal & Leather
Buy It Now 10d 18h -

The 24 Best Net Bags for 2023
Buy It Now 22d 23h -

Louis vuitton pattern, Louis vuitton background, Printable design paper
Buy It Now 5d 8h -

Christian Louboutin So Kate Patent Pump 40 Beige Nude Patent leather ref.743912 - Joli Closet
Buy It Now 15d 20h -

LOUIS VUITTON Montorgueil PM Monogram Canvas Shoulder Bag-US
Buy It Now 13d 13h -

Louis Vuitton Damier Azur Speedy Bandouliere 25 QJB0US0SWB032
Buy It Now 19d 16h -

Goyard 2022 Limited Poitiers "SAC POITIERS CLAIRE VOIE" Mini Tote Shoulder Bag
Buy It Now 2d 13h -

Lauren Conrad apologizes for calling Kristin Cavallari 'slut
Buy It Now 7d 23h -

Designer Bumbags, Fanny Packs, & Belt Bags for Women, Men
Buy It Now 3d 17h -

Your Guide to 8 of the Most Popular Louis Vuitton Bags, Handbags and Accessories
Buy It Now 20d 8h
